Content Delivery Networks — What is a CDN?
01/04/2022Zero Trust security model — what is Zero Trust?
01/04/2022What is A DDoS Attack?
DDoS, or distributed denial of service, is a type of cyberattack that tries to make a website or network resource unavailable by flooding it with malicious traffic so that it is unable to operate.
What is a DDos Attack
DDoS Attack Meaning
In a distributed denial-of-service (DDoS) attack, an attacker overwhelms its target with unwanted internet traffic so that normal traffic can’t reach its intended destination.
But what does that really mean? Imagine your favorite zombie movie. Swarms of infected creatures all with the same goal — to overwhelm civilization as they spread their “zombie plague.” They swamp the resources of law enforcement organizations, deplete military forces, and take down healthcare services. Then, inevitably, there’s a giant traffic jam sprawling as far as the eye can see, as people flee for safety on the highway. That’s what a DDoS attack is like: a zombie apocalypse online. But instead of zombies, hordes of infected computers go after a targeted website, all at the same time — driving humans and business away.
A DDoS attack on a company’s website, web application, APIs, network, or data center infrastructure can cause downtime and prevent legitimate users from buying products, using a service, getting information, or any other access.
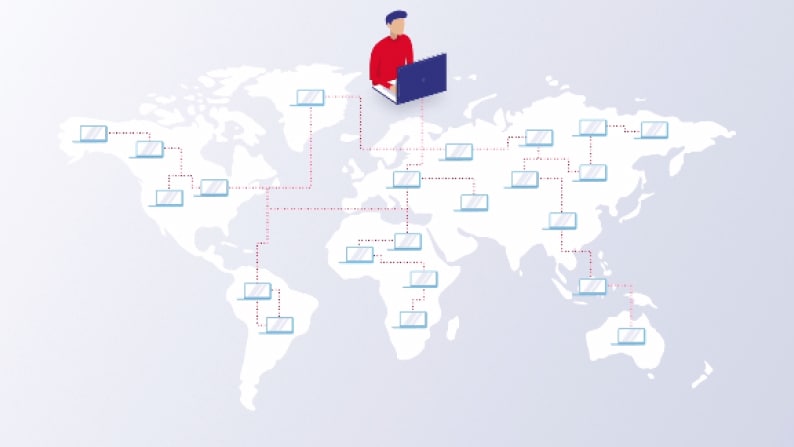
During a DDoS attack, attackers use large numbers of exploited machines and connected devices across the internet. including Internet of Things (IoT) devices, smartphones, personal computers, and network servers to send a flood of traffic to targets.
How does a DDoS Attack Work?
DDoS attacks exploit networks of internet-connected devices to cut off users from a server or network resource, such as a website or application they may frequently access.
To launch a DDoS attack, attackers use malware or take advantage of security vulnerabilities to maliciously infect and gain control over machines and devices. Each computer or infected device, called a “bot” or “zombie,” becomes capable of spreading the malware further and participating in DDoS attacks. These bots form bot armies called “botnets” that leverage their strength in numbers and amplify the size of an attack. And because the infection of IoT devices often goes unnoticed — just like that pesky B movie zombie that you didn’t realize was infected — legitimate device owners become secondary victims or unknowing participants, while attackers remain hard to identify by the victimized organization.
Once an attacker has built a botnet, they are able to send remote instructions to each bot,
directing a DDoS attack on the target system. When a botnet attacks a network or server, the attacker instructs individual bots to send requests to the victim’s IP address. Just as we humans have one-of-a-kind fingerprints, our devices have a unique address that identifies them on the internet or local network. The result of overwhelming traffic leads to a denial of service, preventing normal traffic from accessing the website, web application, API, or network.
Sometimes botnets, with their networks of compromised devices, are rented out for other potential attacks through “attack-for-hire” services. This allows people with malicious intent but no training or experience to easily launch DDoS attacks on their own.

Types of DDoS Attacks
There are many different types of DDoS attacks, and attackers often use more than one type to wreak havoc on their targets. Three key types are volumetric, protocol, and application-layer attacks. The purpose of all attacks is to severely slow down or stop legitimate traffic from reaching its intended destination. For example, this could mean stopping a user from accessing a website, buying a product or service, watching a video, or interacting on social media. Additionally, by making resources unavailable or diminishing performance, DDoS can cause business to grind to a halt. This can result in preventing employees from accessing email, web applications, or conducting business as usual.
To further understand how DDoS attacks work, let’s break down the different pathways attackers can take. The open system interconnection model, also referred to as the “OSI model,” is a layered framework for various networking standards and contains seven different layers. Each layer of the OSI model has a unique purpose, like the floors of an office building where different functions of a business take place on each floor. Attackers target different layers depending on what type of web or internet-facing asset they’d like to disrupt.

The Seven Layers of Network Connectivity in the OSI Model Involved in a DDoS Attack
Layer 7 – Application
The application layer is at the top and is closest to the end user. It’s where people interface with computers and devices and where networks connect with applications.
Layer 6 – Presentation
Data encryption and decryption occur on the presentation layer, enabling secure transmission.
Layer 5 – Session
The session layer allows devices, computers, or servers to communicate with one another and controls ports and sessions.
Layer 4 – Transport
At the transport layer, data is communicated via Transmission Control Protocol (TCP), which is built on top of the Internet Protocol (IP), also called TCP/IP.
Layer 3 – Network
The network layer determines the physical path that data will take to get to its destination.
Layer 2 – Data Link
The data link layer provides a way to transfer data between network entities. It’s also a means to detect and correct errors that can happen in the physical layer.
Layer 1 – Physical
The first and lowest layer, Layer 1 is the physical layer where raw bits are transmitted over a physical data link connecting network nodes.
Volumetric Attacks
The intent of a volume-based DDoS attack is to overwhelm a network with massive amounts of traffic by saturating the bandwidth of the intended victim resource. The large quantities of attack traffic block legitimate users from accessing the application or service, preventing traffic from flowing in or out. Depending on the target, stopping legitimate traffic could mean a bank customer may be unable to pay a bill on time, ecommerce shoppers are unable to complete online transactions, a hospital patient could be barred from their medical records, or a citizen could find themselves unable to view their tax records from a government agency. No matter the organization, blocking people from a service they expect to use online has a negative impact.
Volumetric attacks use botnets created with armies of individual malware-infected systems and devices. Controlled by an attacker, bots are used to cause congestion between a target and the internet at large with malicious traffic that saturates all available bandwidth.
An unforeseen onslaught of bot traffic can significantly slow down or prevent access to a web resource or internet-facing service. Since bots take over legitimate devices to amplify bandwidth-intensive DDoS assaults, often unknowingly to the user, the malicious traffic is difficult for the victimized organization to detect.
Common types of volume-based attacks
There are a variety of volumetric DDoS attack vectors used by threat actors. Many leverage reflection and amplification techniques to overwhelm a target network or service.
UDP Flood
UDP floods are frequently chosen for larger-bandwidth DDoS attacks. Attackers attempt to overwhelm ports on the targeted host with IP packets containing the stateless UDP protocol. The victim host then looks for applications that are associated with the UDP packets, and when not found, sends a “Destination Unreachable” back to the sender. The IP addresses are often spoofed to anonymize the attacker, and once the targeted host becomes inundated with attack traffic, the system becomes unresponsive and unavailable to legitimate users.
DNS reflection/amplification
DNS reflection attacks are a common type of vector where cybercriminals spoof the IP address of their target to send large amounts of requests to open DNS servers. In response, these DNS servers respond back to the malicious requests by the spoofed IP address, thereby creating an attack on the intended target through a flood of DNS replies. Very quickly, the large volume of traffic created from the DNS replies overwhelms the victim organization’s services, making them unavailable and preventing legitimate traffic from reaching its intended destination.
ICMP flood
Internet Control Message Protocol (ICMP) is primarily used for error messaging and typically does not exchange data between systems. ICMP packets may accompany Transmission Control Protocol TCP packets that enable application programs and computing devices to exchange messages over a network, when connecting to a server. An ICMP flood is a Layer 3 infrastructure DDoS attack method that uses ICMP messages to overload the targeted network’s bandwidth.
Protocol Attacks
Protocol attacks attempt to consume and exhaust compute capacity of various network infrastructure resources like servers or firewalls via malicious connection requests that exploit protocol communications. Synchronize (SYN) floods and Smurf DDoS are two common types of protocol-based DDoS attacks. Protocol attacks can be measured in packets per second (pps) as well as bits per second (bps).
SYN flood attack
One of the main ways people connect to internet applications is through the Transmission Control Protocol TCP. This connection requires a three-way handshake from a TCP service — like a web server — and involves sending what is called a SYN (synchronization) packet from where the user connects to the server, which then returns a SYN-ACK (synchronization acknowledgement) packet, that is ultimately answered with a final ACK (acknowledgement) communication back to complete the TCP handshake.
During a SYN flood attack, a malicious client sends a large volume of SYN packets (part one of the usual handshake) but never sends the acknowledgement to complete the handshake. This leaves the server waiting for a response to these half-open TCP connections that eventually run out of capacity to accept new connections for services that track connection states.
A SYN flood attack is like a terrible prank by the entire graduating class of a really big high school, where each student calls the same pizza restaurant and orders a pie during the same time frame. Then, when the delivery person goes to pack up, she realizes that there are too many pizzas to fit in her car and there are no addresses on the orders — so all delivery stops.
Smurf DDoS attack
The name of this DDoS attack is based on the concept that tiny, numerous attackers can overwhelm a much larger opponent by sheer volume, just like the fictional colony of small blue humanoids that are its namesake.
In a Smurf distributed denial-of-service attack large numbers of Internet Control Message Protocol ICMP packets with an intended target’s spoofed source IP are broadcast to a computer network using an IP broadcast address. By default, most devices on a network will respond by sending a reply to the source IP address. Depending on the number of machines on the network, the victim’s computer may be slowed down to a crawl from being flooded with traffic.
Application-layer Attacks
Example: HTTP flood attack
Conducted by flooding applications with malicious requests, application-layer attacks are measured in requests per second (RPS). Also called Layer 7 DDoS attacks, these attacks target and disrupt specific web applications, not entire networks. While difficult to prevent and mitigate, they are among the easier DDoS attacks to launch.
In comparison, it’s easy to startle a herd of horses into a stampede but almost impossible to get them under control again. Application-layer attacks are like that: easy to implement, hard to slow down or stop, and specific to a target.
What are DDoS Attacks Used For?
Distributed denial-of-service DDoS attacks attempt to take down online services, websites, and web applications by flooding them with malicious traffic from multiple sources or exhausting compute resources of the targeted asset. The goal of the attacker is to make the target unavailable to legitimate users, because it’s all about disruption. DDoS attacks target a wide array of resources people depend on every day, including financial services, medical information, news outlets, educational systems, and online shopping.
There are many reasons why threat actors launch DDoS attacks aimed at disrupting organizations. Common motivations can include:
- Hacktivism driven by political or social reasons
- Nation-state attackers aiming to cause economic or social disruption
- Attempts to attract business if a competing service or product is unavailable
- DDoS used as a smokescreen to distract an incident response team from a more elusive, sophisticated attack
- Extortion to drive financial gain and profits
More recently, DDoS extortion attacks in particular have been a popular motivator for cybercriminals. Also known as ransom DDoS (RDDoS) attacks, DDoS extortion attacks happen when threat actor groups (and copycats alike) threaten organizations with a DDoS event unless a ransom or extortion ultimatum is paid. Oftentimes these criminal actors launch a “show-of-force” attack to demonstrate their ability to cause disruption and increase the likelihood of extortion payment by the targeted company. To avoid being caught, attackers insist on payment in cryptocurrency, like Bitcoin.
Like an elementary school kid that a bully steals homework from, then makes him give over his lunch money to get it back, DDoS extortion attacks are all about ransom. In the sophisticated world of online bullying, the ransom money is digital and untraceable.

How to Defend Against DDoS Attacks
With a strong DDoS strategy and runbook in place, organizations can protect against and limit disruption from DDoS attacks. The high-capacity, high-performance, and always-on anti-DDoS protection of cloud-based solutions can prevent malicious traffic from reaching a website or interfering with communication by a web API. A cloud-based scrubbing service can quickly mitigate attacks that target non-web assets, like network infrastructure, at scale.

DDoS protection
In a constantly evolving attack landscape, DDoS protection through a mitigation provider that takes a defense-in-depth approach can keep organizations and end users safe. A DDoS mitigation service will detect and block DDoS attacks as quickly as possible, ideally in zero or a few seconds from the time that the attack traffic reaches the mitigation provider’s scrubbing centers. Because attack vectors keep changing and attack sizes keep getting bigger, to achieve the best DDoS protection a provider must continually invest in defense capacity. To keep up with large, complex attacks, the right technologies are needed to detect malicious traffic and begin robust defensive countermeasures to mitigate attacks quickly.
DDoS mitigation providers filter out malicious traffic to prevent it from reaching the intended targeted asset. Attack traffic is blocked by a DDoS scrubbing service, a cloud-based DNS service, or a CDN-based web protection service. Cloud-based mitigation removes attack traffic before it reaches the target.
DDoS cloud scrubbing
DDoS scrubbing can keep your online business up and running, even during an attack. Unlike CDN-based mitigation, a DDoS scrubbing service can protect across all ports, protocols, and applications in the data center, including web- and IP-based services. Organizations direct their network traffic in one of two ways: via a Border Gateway Protocol (BGP) route advertisement change or DNS redirection (A record or CNAME) to the mitigation provider’s scrubbing infrastructure. Traffic is monitored and inspected for malicious activity, and mitigation is applied if DDoS attacks are identified. Typically, this service can be available in both on-demand and always-on configurations, depending on an organization’s preferred security posture — although more organizations than ever before are moving to an always-on deployment model for the fastest defensive response.
CDN-based defense
A properly configured advanced content delivery network (CDN) can help defend against DDoS attacks. When a website protection service provider uses its CDN to specifically accelerate traffic using HTTP and HTTPS protocols, all DDoS attacks targeting that URL can then be dropped at the network edge. This means that Layer 3 and Layer 4 DDoS attacks are instantly mitigated, as this type of traffic is not destined for web ports 80 and 443. As a cloud-based proxy, the network sits in front of a customer’s IT infrastructure and delivers traffic from end users to the websites and applications. Because these solutions operate in-line, web-facing assets are protected at all times without human interaction from network-layer DDoS attacks. For application layer–specific defense, organizations should look to deploy a web application firewall to combat advanced attacks, including certain types of DDoS attacks like HTTP GET and HTTP POST floods, which aim to disrupt Layer 7 application processes of the OSI model.
The benefits of DDoS mitigation services
Organizations can reduce their attack surface while also reducing risk of business-impacting downtime and disruption by deploying DDoS-specific security controls. This type of defense can thwart an attack while allowing legitimate visitors to access your organization online as they normally would. DDoS protection prevents malicious traffic from reaching its target, limiting the impact of the attack, while allowing normal traffic to get through for business as usual.
How can you stop a DDoS attack?
During mitigation, your DDoS protection provider will deploy a sequence of countermeasures aimed at stopping and diminishing the impact of a distributed denial-of-service DDoS attack. As modern attacks become more and more advanced, cloud-based DDoS mitigation protection helps to provide defense-in-depth security at scale, keeping back-end infrastructure and internet-facing services available and performing in an optimal manner.
Through DDoS attack protection services, organizations can:
- Reduce the attack surface and business risk associated with DDoS attacks
- Prevent business-impacting downtime
- Increase speed to respond to a DDoS event and optimize incident response resources
- Shorten the time to understand and investigate a service disruption
- Prevent loss of employee productivity
- More quickly deploy countermeasures to defend against a DDoS attack
- Prevent damage to brand reputation and bottom line
- Maintain application uptime and performance across digital estates
- Minimize costs associated with web security
- Defend against new and evolving threats
Learn how Akamai can help protect your web and internet-facing services from DDoS attacks
How a holistic DDoS defense works
Akamai provides DDoS defense in depth through a transparent mesh of dedicated edge, distributed DNS, and cloud scrubbing defenses. These purpose-built cloud solutions are designed to strengthen DDoS security postures while reducing attack surfaces, improving the quality of mitigation, and reducing false positives, while increasing resiliency against the largest and most complex attacks.
Moreover, the solutions can be fine-tuned to the specific requirements of your web applications and internet-based services.
Edge Defense
Akamai architected its globally distributed intelligent edge platform as a reverse proxy to only accept traffic via ports 80 and 443. All network-layer DDoS attacks are instantly dropped at the edge with a zero-second SLA. That means that attackers launching network-layer DDoS attacks don’t stand a chance.
For application-layer DDoS attacks, including those launched via APIs, Kona Site Defender detects and mitigates the attacks, while simultaneously granting access to legitimate users.
DNS Defense
Akamai’s authoritative DNS service, Edge DNS, also filters traffic at the edge. Unlike other DNS solutions, Akamai specifically architected Edge DNS for availability and resiliency against DDoS attacks. Edge DNS also delivers superior performance, with architectural redundancies at multiple levels, including name servers, points of presence, networks, and even segmented IP Anycast clouds.
Cloud Scrubbing Defense
Prolexic protects entire data centers and hybrid infrastructures from DDoS attacks, across all ports and protocols, with 20 global scrubbing centers and more than 10 Tbps of dedicated DDoS defense. This capacity is designed to keep internet-facing assets available — a cornerstone of any information security program.
As a fully managed service, Prolexic can build both positive and negative security models. The service combines automated defenses with expert mitigation from Akamai’s global team of 225+ frontline SOCC responders. Prolexic also offers an industry-leading zero-second mitigation SLA via proactive defensive controls to keep data center infrastructure and internet-based services protected and highly available.
