Akamai Guardicore Segmentation
Phân đoạn vi mô nhanh chóng và trực quan cho mọi môi trường.
Ngăn chặn lây lan lân cận nhờ chức năng điều khiển chi tiết
Phân đoạn Akamai Guardicore là giải pháp phân đoạn vi mô dựa trên phần mềm đơn giản, nhanh chóng và trực quan nhất để thực hiện các nguyên tắc Zero Trust. Giải pháp này cho phép ngăn chặn hiện tượng lây lan lân cận có hại trong mạng lưới thông qua các chính sách phân đoạn nghiêm ngặt, tính trực quan của hoạt động trong môi trường CNTT và cảnh báo an ninh mạng. Phân đoạn Akamai Guardicore hoạt động trên các trung tâm dữ liệu, môi trường đa đám mây và điểm cuối với tốc độ triển khai nhanh hơn so với các phương pháp phân đoạn cơ sở hạ tầng và đem đến khả năng hiển thị cũng như kiểm soát mạng vượt trội.
Cách thức hoạt động?
Bằng cách sử dụng kết hợp các cảm biến dựa trên tác nhân, trình thu thập dữ liệu dựa trên mạng và nhật ký luồng đám mây riêng ảo để ánh xạ mạng của bạn, Phân đoạn Akamai Guardicore được thiết kế để cung cấp một hình ảnh trực quan duy nhất về toàn bộ tài sản và cơ sở hạ tầng của bạn – bao gồm hệ điều hành cũ và hệ điều hành hiện đại, công nghệ vận hành và thiết bị Internet Vạn vật (IoT). Từ đó, bạn có thể dễ dàng tạo và thực hiện các chính sách giúp hạn chế bề mặt tấn công và đáp ứng nhu cầu kinh doanh của bản thân.
Phương thức lý tưởng hơn để đạt tới phân đoạn Zero Trust
Giảm thiểu phơi nhiễm với các cuộc tấn công
Giảm thiểu rủi ro mà không cần phần cứng bảo mật tốn kém nhờ phương pháp phân đoạn vi mô dựa trên phần mềm.
Ngăn chặn lây lan lân cận
Phát hiện lây lan lân cận và các mối đe dọa theo thời gian thực trên toàn bộ chuỗi tiêu diệt tấn công mạng bằng một nền tảng duy nhất.
Bảo mật tài sản CNTT quan trọng
Bảo vệ tài sản quan trọng khỏi mã độc tống tiền bằng cách dễ dàng thực hiện nguyên tắc Zero Trust trên các hệ sinh thái đám mây kết hợp.
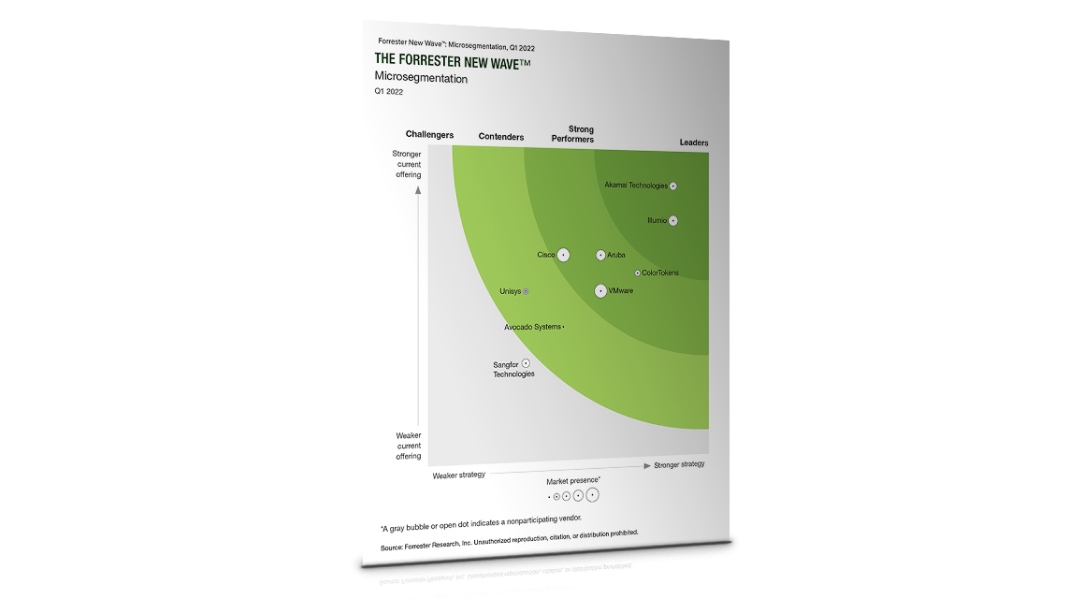
Tìm hiểu lý do Forrester gọi Phân đoạn Akamai Guardicore là Giải pháp đi đầu
Tính năng
- Khả năng phân đoạn chi tiết thành các quy trình và dịch vụ riêng lẻ
- Khả năng hiển thị lịch sử và gần thời gian thực giúp phân tích điều tra trở nên dễ dàng hơn
- Phạm vi nền tảng rộng nhất cho cả công nghệ cũ và hệ thống mới nhất
- Dịch vụ săn tìm mối đe dọa tùy chỉnh do Nghiên cứu Bảo mật Akamai cung cấp.
- Ghi nhãn tài sản linh hoạt tích hợp với hệ thống điều phối và cơ sở dữ liệu quản lý cấu hình (Configuration management database, CMDB)
- Tạo chính sách nhanh chóng và trực quan với mẫu thiết kế sẵn cho các trường hợp sử dụng phổ biến nhất
- Tình báo mối đe dọa và phát hiện vi phạm nhằm giảm thời gian ứng phó sự cố

4 lý do tại sao doanh nghiệp bạn cần Kiến trúc Zero Trust
Câu hỏi thường gặp (FAQ)
Giải pháp này có sẵn trên đám mây hoặc phần mềm tại chỗ, cho phép bạn dễ dàng triển khai chiến lược phân đoạn mạng vào kiến trúc hiện tại của mình.
Có, bạn có thể chạy tường lửa của mình song song với giải pháp phân đoạn vi mô của Akamai. Tuy nhiên, Phân đoạn Akamai Guardicore là giải pháp phân đoạn mạng linh hoạt và chi tiết hơn nên bạn có thể loại bỏ hầu hết các tường lửa, đặc biệt là các tường lửa nội bộ. Nhiều khách hàng cũng chạy song song tường lửa và Phân đoạn Akamai Guardicore trong khoảng thời gian ngắn cho đến khi họ cảm thấy yên tâm với việc thực hiện chính sách mới.
Giải pháp phân đoạn vi mô của chúng tôi là giải pháp dựa trên tác nhân. Chúng tôi cũng có phiên bản không tác nhân dành cho các thiết bị không thể cài đặt phần mềm (chẳng hạn như thiết bị IoT), mang lại sự linh hoạt để bạn có thể bảo vệ tất cả máy chủ, tài sản Linux, Windows và Mac của mình. Giải pháp của chúng tôi hỗ trợ hầu hết mọi thứ, từ các hệ thống cũ cho đến các hệ điều hành hiện đại, bao gồm Windows 7, 2000, 8 và Kubernetes (K8s).
Bạn có thể tạo chính sách một cách nhanh chóng và dễ dàng. Với AI, giải pháp phân đoạn vi mô của chúng tôi đề xuất các chính sách thông qua mẫu và quy trình làm việc trực quan, đồng thời cho phép bạn tùy chỉnh chúng dựa trên nhu cầu kinh doanh của riêng mình.
Đây là một sản phẩm phân đoạn vi mô độc lập giúp bảo vệ lưu lượng truy cập giữa các máy chủ và thực hiện một trong những nguyên tắc cốt lõi của Zero Trust, như được định nghĩa bởi Forrester® và Gartner®. Forrester khẳng định rằng “Phân đoạn vi mô là yếu tố thiết yếu cho mạng cá nhân Zero Trust” trong Forrester New Wave™ năm 2022.
Akamai cung cấp các dịch vụ săn tìm mối đe dọa được quản lý thông qua Akamai Hunt, giúp tìm và khắc phục các rủi ro bảo mật khó tránh nhất trong môi trường của bạn. Dịch vụ được dẫn dắt bởi các chuyên gia bảo mật từ các nhóm phân tích và tình báo mối đe dọa của Akamai – đồng thời sử dụng dữ liệu được thu thập từ giải pháp Phân đoạn Akamai Guardicore – để tìm kiếm các mối đe dọa trong mạng của bạn, tìm và vá các lỗ hổng ảo, cũng như củng cố cơ sở hạ tầng của bạn.

“Phân đoạn Akamai Guardicore đã vượt qua tất cả các giải pháp khác mà chúng tôi từng thấy nhờ việc dễ dàng triển khai trên quy mô lớn cùng khả năng đem đến cho người dùng cái nhìn sâu hơn về những gì đang xảy ra bên trong mạng của mình. Khả năng tìm kiếm người dùng để biết vị trí của họ và những việc họ đang làm có giá trị vô cùng lớn trong việc phòng chống mã độc tống tiền.”
Shane Barnard, Senior Network Engineer, Summit Hosting
Các use case phân đoạn vi mô
Tìm hiểu cách phân đoạn vi mô cung cấp khả năng khoanh vùng ứng dụng quan trọng, kiểm soát quyền truy cập của bên thứ ba, khả năng tương thích với đám mây AWS, bảo mật vùng chứa Docker và Kubernetes, phát hiện và ứng phó với mối đe dọa và quản lý chính sách phân đoạn Zero Trust.
Khoanh vùng ứng dụng quan trọng
Bảo vệ tập trung các ứng dụng mà bạn dựa vào nhiều nhất
Hầu hết các tổ chức đều có một bộ ứng dụng chọn lọc giữ vai trò cốt lõi xuyên suốt trong mọi hoạt động kinh doanh của họ, từ các ứng dụng web dành cho khách hàng đến cơ sở dữ liệu chứa thông tin nhạy cảm hoặc có giá trị. Những sự cố bảo mật ảnh hưởng đến các loại tài sản quan trọng này có thể tác động đáng kể đến hoạt động kinh doanh và danh tiếng của công ty. Akamai giúp đội ngũ bảo mật cung cấp trọng tâm bảo mật cần thiết cho các ứng dụng quan trọng bằng cách đưa ra bản đồ trực quan về cách chúng hoạt động để dễ dàng khoanh vùng bằng chính sách phân đoạn cụ thể, phát hiện và ngăn chặn các cuộc tấn công có chủ đích.
Ưu điểm:
- Trực quan hóa chi tiết các ứng dụng quan trọng – Hiểu cách các ứng dụng này hoạt động và giao tiếp nhằm bảo vệ một cách hiệu quả.
- Tạo chính sách khoanh vùng chi tiết – Kiểm soát chặt chẽ cách các ứng dụng hoạt động và cách ly chúng ở mức độ cao nhất.
- Phát hiện và ứng phó với các cuộc tấn công một cách nhanh chóng – Sử dụng nhiều kỹ thuật bổ sung để phát hiện và giảm thiểu các cuộc tấn công nhằm vào tài sản quan trọng.
Kiểm soát truy cập của bên thứ ba
Quản lý chặt chẽ quyền truy cập tài nguyên CNTT dựa trên nhu cầu kinh doanh
Phân đoạn Akamai Guardicore đem đến khả năng hiển thị và kiểm soát chính xác quyền truy cập của bên thứ ba vào môi trường CNTT của bạn. Khả năng trực quan hóa ứng dụng mạnh mẽ của Akamai kết hợp các nhãn ngữ cảnh từ các công cụ điều phối và nguồn dữ liệu khác để giúp bạn dễ dàng hiểu rõ chức năng của các ứng dụng cụ thể. Với những thông tin chuyên sâu này, đội ngũ bảo mật có thể triển khai các chính sách chi tiết giúp giới hạn quyền truy cập ứng dụng ở những người dùng và nhóm Active Directory cụ thể. Việc này cho phép các tổ chức hỗ trợ nhu cầu truy cập của bên thứ ba trong khi hạn chế khả năng xâm nhập bảo mật.
Ưu điểm:
- Xem các ứng dụng theo chức năng – Xem các ứng dụng và hoạt động giao tiếp của chúng theo ngữ cảnh trên bản đồ trực quan có thể tùy chỉnh.
- Kiểm soát quyền truy cập của người dùng bên thứ ba – Giới hạn quyền truy cập của người dùng. Chỉ cho phép họ truy cập vào những ứng dụng cần thiết cho nhu cầu kinh doanh rõ ràng của họ.
- Phát hiện hành vi lạm dụng tài khoản người dùng tiềm ẩn – Nhận cảnh báo kịp thời và thông tin hỗ trợ khi ai đó cố gắng sử dụng tài khoản trái phép.
Giải pháp phân đoạn vi mô AWS
Đơn giản hóa mô hình trách nhiệm chung với bảo mật đám mây AWS
Akamai là Đối tác công nghệ cao cấp cho phân đoạn vi mô AWS với năng lực bảo mật. Là một công cụ bên thứ ba mạnh mẽ, Phân đoạn Akamai Guardicore tận dụng khả năng hiển thị sâu để ánh xạ toàn bộ cơ sở hạ tầng CNTT, hoạt động giao tiếp và các phần phụ thuộc theo cách trực quan. Bản đồ này hỗ trợ cơ sở hạ tầng đám mây kết hợp và đa đám mây, giúp các nhóm đảm bảo duy trì trạng thái bảo mật và xác nhận rằng họ hiểu cách các ứng dụng và môi trường tương tác cũng như phụ thuộc lẫn nhau. Đồng thời, giải pháp này còn cung cấp cơ sở để xây dựng chính sách bảo mật phân đoạn vi mô thông minh, linh hoạt và chặt chẽ. Tóm lại, Akamai giúp việc quản lý và bảo trì mô hình trách nhiệm chung của đám mây AWS trở nên đơn giản.
Ưu điểm:
- Giải pháp phân đoạn vi mô tích hợp đầy đủ cho AWS cho phép người dùng xem thông tin đám mây gốc và dữ liệu dành riêng cho AWS trên bảng điều khiển.
- Khả năng hiển thị chi tiết ở cấp quy trình giúp tăng khả năng hiển thị đến cấp quy trình cho các phiên bản của bạn.
- Đưa phân đoạn vi mô của bạn vượt ra ngoài AWS bằng các chính sách phân đoạn vi mô đơn giản trải rộng trên các khu vực và đám mây riêng ảo (VPC), vùng chứa, máy ảo (VM) và các phần mềm tại chỗ.
Container Security
Giải pháp bảo mật liền mạch toàn diện cho các ứng dụng được đóng gói
Phân đoạn Akamai Guardicore cung cấp khả năng bảo mật vùng chứa toàn diện cho các nhóm sử dụng tổ hợp bất kỳ giữa Docker và Kubernetes. Akamai bảo vệ các ứng dụng được đóng gói, trao quyền cho các nhóm DevSecOps với nhiều tính năng quan trọng khác nhau mà không ảnh hưởng tới tình trạng bảo mật của tổ chức. Akamai bảo đảm các yếu tố sản xuất và vận hành của vùng chứa bằng cách cho phép khả năng hiển thị trong mọi vùng chứa, trực quan hóa các luồng giao tiếp và bảo mật bằng các chính sách phân đoạn vi mô.
Ưu điểm:
- Có được khả năng hiển thị và khám phá mọi luồng giao tiếp trong nhóm vùng chứa và trong vùng chứa.
- Áp dụng các chính sách phân đoạn dựa trên nhãn nhóm vùng chứa gốc để đảm bảo quy mô kiểm soát bảo mật và di chuyển với vùng chứa.
- Bảo vệ các ứng dụng được đóng gói trong khối lượng công việc nhạy cảm với PCI và thể hiện sự tuân thủ.
Phát hiện và ứng phó với mối đe dọa
Phát hiện các mối đe dọa nhanh hơn và ứng phó thông minh hơn
Ngày nay, các đám mây và trung tâm dữ liệu đang mở rộng nhanh chóng đã trở thành mục tiêu chính cho các cuộc xâm nhập và tấn công với tần suất đáng báo động. Đội ngũ bảo mật đang phải nỗ lực rất nhiều để bắt kịp với tỷ lệ vi phạm đáng kinh ngạc này. Phân đoạn Akamai Guardicore là giải pháp phân đoạn vi mô duy nhất cung cấp một nền tảng đơn nhất có thể mở rộng với khả năng phát hiện và ứng phó mối đe dọa theo thời gian thực, với các thuộc tính chính sau:
- Nhiều phương pháp phát hiện
- Được thiết kế riêng cho đám mây
- Tích hợp khả năng ứng phó
- Điều tra chi tiết
Ưu điểm:
- Nhiều phương pháp phát hiện giúp giải quyết tất cả các mối đe dọa.
- Điều tra các mối đe dọa bằng phân tích tự động và dữ liệu về sự cố có độ chính xác cao.
- Ứng phó với các cuộc tấn công bằng các đề xuất giảm thiểu trong khi các yếu tố tích hợp trong nền tảng tăng tốc hoạt động ứng phó sự cố.
Zero Trust Segmentation
Khám phá các phần phụ thuộc của ứng dụng để giảm bề mặt tấn công, bảo vệ các ứng dụng quan trọng và đảm bảo tuân thủ
Một nền tảng vững chắc để tuân thủ và bảo vệ khối lượng công việc cần có khả năng cách ly và phân đoạn chi tiết các ứng dụng mạng của bạn cùng thành phần của chúng. Phân đoạn Akamai Guardicore cho phép các phần phụ thuộc sâu của ứng dụng ánh xạ và thực hiện chính sách, đảm bảo quá trình quản lý liên tục chính sách phân đoạn vi mô của bạn. Đây là một trong những giải pháp hoàn chỉnh và linh hoạt nhất trong ngành cho phân đoạn vi mô, với các thuộc tính chính sau:
- Phạm vi rộng
- Khả năng hiển thị sâu
- Quy trình làm việc trực quan
- Chính sách chi tiết
Ưu điểm:
- Hiển thị môi trường của bạn thông qua khám phá ứng dụng và ánh xạ phần phụ thuộc để phân biệt được yếu tố đáng và không đáng tin cậy.
- Thực hiện các nguyên tắc Zero Trust với chính sách thiết kế, thử nghiệm và triển khai nhanh.
- Theo dõi và giám sát mạng của bạn bằng tình báo mối đe dọa, cảnh báo, v.v.
Bảo mật thiết bị IoT
Zero Trust cho Thiết bị được kết nối
Bảo mật thiết bị IoT/OT ở quy mô lớn
Bảo mật các thiết bị IoT và OT đã luôn là một thách thức đối với hầu hết các tổ chức. Với Phân đoạn Akamai Guardicore, giờ đây, các tổ chức đã có thể thu hẹp bề mặt tấn công của họ và thực hiện chính sách Zero Trust trên các thiết bị không thể chạy phần mềm bảo mật dựa trên máy chủ. Các tính năng chính bao gồm:
- Phát hiện thiết bị liên tục
- Tích hợp khả năng lấy dấu vân tay thiết bị
- Khả năng hiển thị sâu
- Phân đoạn Zero Trust không tác nhân
- Nhận biết thiết bị chuyển vùng
Ưu điểm:
- Khám phá, trực quan hóa và ánh xạ tất cả các hệ thống IoT và OT cùng cơ sở hạ tầng CNTT của bạn trong một chế độ xem duy nhất.
- Xác định và phân đoạn hệ thống có giá trị cao nhằm bảo vệ chúng khỏi sự lây lan của các vi phạm. Không cần công cụ bảo mật bên thứ ba.
- Chỉ định dấu vân tay riêng cho mỗi thiết bị nhằm đảm bảo rằng các chính sách bảo mật phù hợp được áp dụng.
- Ngăn chặn và cách ly mã độc tống tiền cũng như các cuộc tấn công bằng phần mềm độc hại khác bằng cách áp dụng các chính sách phân đoạn có đặc quyền thấp nhất cho mạng trước khi xảy ra cuộc tấn công.
- ccurs.